Custom Blockchain Architecture Explained: Build Secure & Scalable Solutions
As organizations continue to digitize their operations, the need for secure, transparent, and scalable systems has become more critical than ever. Blockchain technology has emerged as a powerful solution, enabling businesses to build decentralized ecosystems that enhance trust and efficiency. However, the effectiveness of any blockchain solution depends heavily on its underlying architecture.
Custom blockchain development focuses on designing blockchain architectures according to specific business requirements rather than relying on generic, pre-built frameworks. This customization ensures that the system aligns with organizational workflows, regulatory requirements, and long-term scalability goals.
At its core, blockchain architecture defines how data is structured, validated, stored, and shared across a decentralized network. It determines how different components, such as nodes, consensus mechanisms, and smart contracts, interact with each other.
For businesses and startups, understanding blockchain architecture is not just a technical necessity; it is a strategic advantage. A properly designed architecture enables faster transactions, seamless integrations, and the ability to scale as the business grows. On the other hand, a poorly designed system can lead to inefficiencies, security risks, and increased operational costs.
Core Components of Blockchain Systems
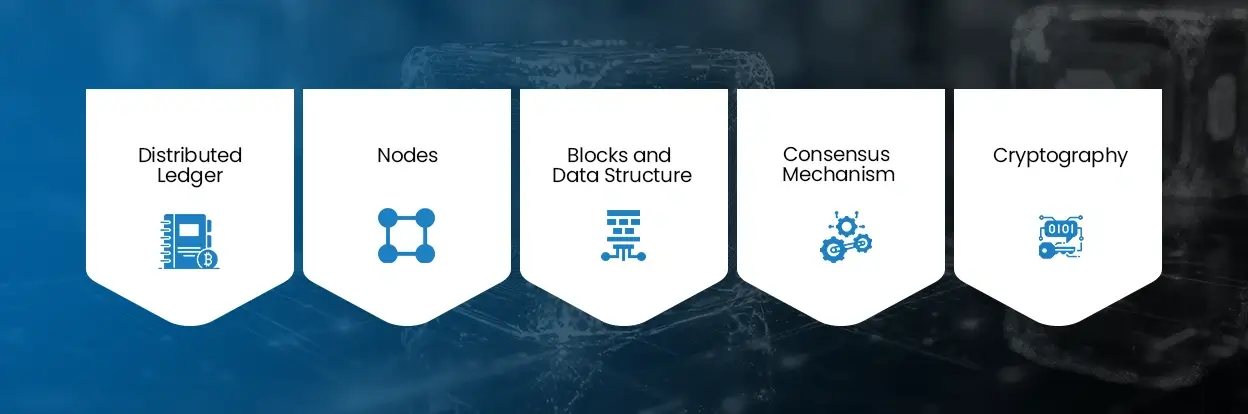
To build effective enterprise blockchain solutions, understand the core components that structure a blockchain system. These components work together to ensure data integrity, transparency, and security.
1. Distributed Ledger
The distributed ledger is the foundation of any blockchain system. It is a shared database that is replicated across multiple nodes in the network. Unlike traditional centralized databases, there is no single point of control or failure.
Every transaction is recorded in the ledger and is visible to all participants, depending on access permissions. This transparency builds trust among stakeholders and reduces the risk of data manipulation.
Additionally, once data is recorded on the blockchain, it becomes immutable, meaning it cannot be altered or deleted. This ensures a permanent and reliable record of all transactions.
2. Nodes
Nodes are the backbone of a blockchain network. They are responsible for maintaining the ledger, validating transactions, and ensuring the system’s integrity.
Different types of nodes serve different purposes:
- Full Nodes store the complete blockchain data and validate transactions independently.
- Light Nodes store only essential data, making them faster and more efficient.
- Validator Nodes participate in consensus mechanisms to confirm transactions.
The distribution and configuration of nodes directly impact the performance, decentralization, and security of the blockchain network.
3. Blocks and Data Structure
Transactions are grouped into blocks, which are then linked together to form a chain. Each block contains:
- Transaction details
- Timestamp
- Cryptographic hash of the previous block
This structure ensures that any attempt to alter a block would require changes to all subsequent blocks, making the system highly secure and tamper-resistant.
4. Consensus Mechanism
Consensus mechanisms are critical for maintaining trust in a decentralized system. They ensure that all nodes agree on the validity of transactions before adding to the blockchain. Common consensus mechanisms include:
- Proof of Work (PoW): Highly secure but resource-intensive
- Proof of Stake (PoS): More energy-efficient and scalable
- Delegated Proof of Stake (DPoS): Faster and more efficient
- Practical Byzantine Fault Tolerance (PBFT): Ideal for enterprise use
Choosing the right consensus mechanism is a major decision in blockchain application development, as it affects speed, cost, and security.
5. Cryptography
Cryptography ensures the security and integrity of blockchain systems. It protects data from unauthorized access and ensures that transactions are verified securely. Key cryptographic elements include:
- Hashing algorithms
- Public and private key encryption
- Digital signatures
These mechanisms ensure that only authorized users can access and modify data, making blockchain systems highly secure.
Types of Blockchain Networks
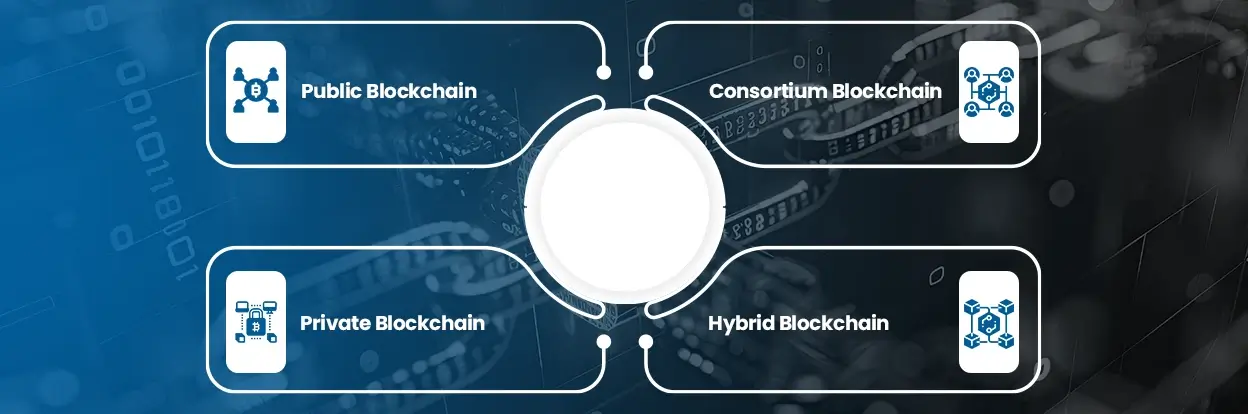
Selecting the right network type is crucial when designing enterprise blockchain solutions, as it determines how data is shared and who can participate.
1. Public Blockchain
Public blockchains are open networks where anyone can join and participate. They offer high transparency and decentralization.
Advantages:
- Fully transparent
- Highly secure
- No central authority
Challenges:
- Slower transaction speeds
- Higher energy consumption
Public blockchains are ideal for decentralized applications and open ecosystems.
2. Private Blockchain
A single organization controls the private blockchains. Access is restricted, and only authorized participants can interact with the network.
Benefits:
- Faster transactions
- Greater control
- Enhanced data privacy
These are widely used in enterprise environments where confidentiality is critical.
3. Consortium Blockchain
A group of organizations manages the Consortium blockchain. They offer a balance between decentralization and control.
Use cases include:
- Financial institutions
- Supply chain networks
- Industry collaborations
This model is ideal for businesses that need shared control without full public access.
4. Hybrid Blockchain
Hybrid blockchains combine elements of both public and private networks. Businesses can keep sensitive data private while making certain information publicly accessible. This flexibility makes hybrid models suitable for complex business environments requiring both transparency and privacy.
Smart Contract Architecture
Smart contracts are a key component of custom blockchain services, enabling automation and efficiency in business processes.
1. Structure of Smart Contracts
Smart contracts consist of:
- Predefined rules and conditions
- Business logic
- Execution protocols
Once deployed, they execute automatically when conditions are met.
2. Architectural Layers
Smart contract systems typically include:
- Application Layer: User interface interacting with the blockchain
- Contract Layer: Core logic and execution
- Data Layer: Storage of contract-related data
Each layer must be optimized for performance and security.
3. Business Benefits
- Eliminates intermediaries
- Reduces operational costs
- Speeds up transactions
- Enhances transparency
4. Security Considerations
Since smart contracts are immutable, any vulnerability can lead to significant risks. Regular audits and testing are essential to ensure reliability.
Security Layers in Blockchain Systems
Security is often considered one of the strongest advantages of blockchain technology, but it is important to understand that this security does not come automatically. It is the result of a well-planned and properly implemented architecture. Security is usually centralized, meaning a single point of failure can compromise the entire network in traditional systems.
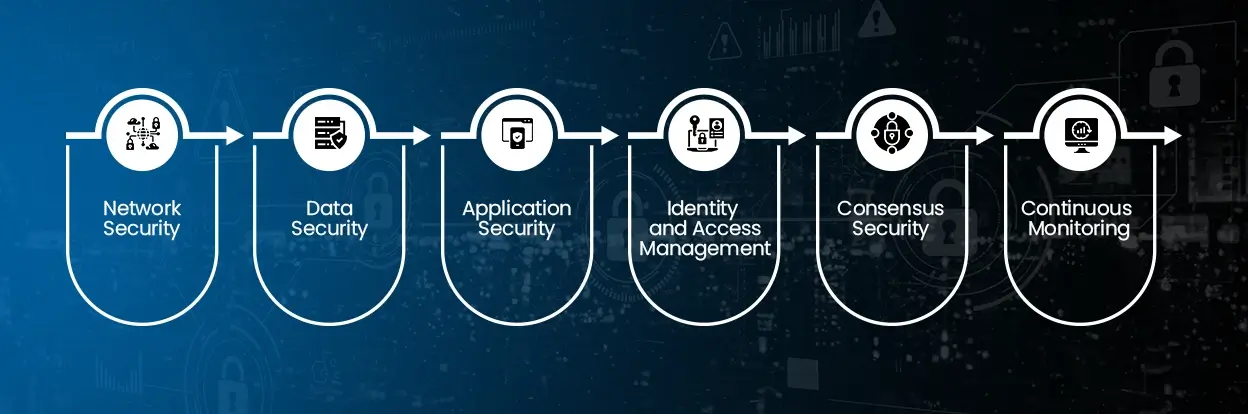
1. Network Security
At the foundation, blockchain networks are designed to resist external attacks. Decentralization plays a key role here, as there is no single server that attackers can target. Each node independently verifies transactions, making it extremely difficult for malicious actors to manipulate the system.
2. Data Security
Blockchain ensures data integrity through cryptographic hashing. Each block is linked to the previous one using a unique hash, creating a secure chain. If any data within a block is altered, the hash changes, immediately signaling tampering.
3. Application Security
Application security in blockchain refers to protecting the software layer built on top of the blockchain, including decentralized applications (dApps), user interfaces, APIs, and integrations with external systems. While the blockchain network itself is inherently secure due to cryptography and decentralization, the applications interacting with it can still be vulnerable if not properly designed.
4. Identity and Access Management
Identity and Access Management (IAM) is a critical security layer in blockchain systems, especially for enterprise blockchain solutions where multiple stakeholders interact with sensitive data. While public blockchains are open, most business use cases rely on permissioned networks where access needs to be controlled and monitored.
5. Consensus Security
Consensus mechanisms act as a security layer by validating transactions before they are added to the blockchain. They prevent fraudulent activities such as double-spending or unauthorized changes. Different consensus models provide different levels of security:
- Proof of Work ensures high security through computational effort.
- Proof of Stake reduces energy consumption while maintaining trust.
- PBFT ensures fast and secure validation in enterprise environments
6. Continuous Monitoring
Continuous monitoring is the process of actively observing and analyzing blockchain systems in real time to detect potential threats, performance issues, or unusual activities. While blockchain is inherently secure, it is not immune to risks, especially at the application and integration layers. This layer ensures that the system remains secure.
Scalability & Performance Optimization
Scalability is a key challenge in blockchain systems. Businesses need solutions that can grow with their operations.
- Layer 2 Solutions: Technologies like sidechains and state channels reduce the load on the main blockchain, improving scalability.
- Sharding: Sharding divides the network into smaller segments, allowing parallel processing and faster transactions.
- Efficient Consensus Mechanisms: Using energy-efficient consensus methods improves speed and reduces costs.
- Off-Chain Storage: Storing large datasets off-chain improves performance while maintaining blockchain integrity.
- Infrastructure Optimization: Using cloud infrastructure and optimized node configurations ensures better performance and reliability.
FAQs
What architecture does blockchain use?
Blockchain uses a decentralized, distributed architecture where data is stored across multiple nodes, ensuring transparency and security.
How secure is blockchain infrastructure?
Blockchain is highly secure due to cryptography, decentralization, and consensus mechanisms. However, proper implementation is key.
What consensus mechanism is best?
The best mechanism depends on the use case. PoS is scalable, while PBFT is ideal for enterprise environments.
Can blockchain handle enterprise-scale data?
Yes, with techniques like sharding, Layer 2 solutions, and optimized architecture, blockchain can handle large-scale data efficiently.
Conclusion
Understanding blockchain architecture is essential for businesses aiming to build secure and scalable decentralized systems. A well-designed architecture ensures efficiency, reliability, and long-term success.
Customized blockchain enables organizations to create tailored solutions that align with their business goals. By focusing on the right architecture, businesses can unlock the full potential of blockchain technology.
As adoption continues to grow, companies investing in strong architectural foundations will gain a competitive advantage in the evolving digital landscape.
Insights Are Valuable & Execution is Priceless
You’ve read about the digital future. Now, let’s build the infrastructure to take you there. Move your strategy from the page to the product.
Design Your Solution Now